Monitoring Software-as-a-Service (SaaS) cloud solutions with QRadar
One of the big advantages of having a Software-As-A-Service (SaaS) solution is the fact you don’t need to worry about infrastructure issues, such as patching, network availability, and etc. Also, most of the companies assume that all the security aspects of the solution will be handled by the vendor. Indeed, the vendor is (or should be) responsible for ensuring their system is secure, but it’s important to note that we should still monitor the SaaS solution for hacking attempts, which can be done through QRadar.
Picture this: imagine you have your website on wordpress, you pay wordpress as a service so you don’t need to worry about patching or updates. In theory, the wordpress team also monitors if someone tries to perform an attack against your site (for example, a SQL injection). But let’s say a malicious actor finds out the password of one of your wordpress users and creates a backdoor account for later exploitation. It wouldn’t be flagged by the wordpress security team (since it’s just a new user being created). That’s where QRadar can add value. If you integrate your wordpress with your QRadar solution, you would be able to generate an alert to your system administrator when a user is created or even correlate this event with other events such as pages being modified.
The easiest way to integrate your SaaS with QRadar is through email alerts from your SaaS solution. Let’s take the WordPress example and put it into a step-by-step:
- Install the WordPress “Security Audit log” plugin
- Create a mailbox to receive the alerts
- Create a script that reads your mailbox and saves into a file. For example, you can modify this script to achieve that.
- Create a custom DSM parser that interprets the file generated by the script above.
- Create a log source on QRadar that monitors the file created by the script mentioned on step three. Use the custom DSM on this log source.
The implementation may require some time in the first time, but after setting up your first SaaS it will be trivial to set up the second one (since you will already have the mailbox set up and the script that reads the file). The same step by step can be adapted for a number of other SaaS services, such as: Dropbox, Gmail, Office365, Salesforce, AWS Cloudtrail and CloudWatch, etc…
Some of the events that can be interesting for us: New accounts created, change on security settings, login out of business hours, bruteforce attacks, configuration changes, etc.
Monitoring your SaaS solutions will put you one step ahead, ensuring that even applications on the cloud are being monitored and secure. Remember, even the server not being in your datacentre, the data in a SaaS application still yours.
Monitoring Cloud Servers with QRadar
Cloud computing is an inevitable upward trend. Companies are looking for all the benefits cloud computing, such as cost effectiveness and scalability, but they may be neglecting the need of event monitoring in a cloud environment.
Configuring a SIEM solution to collect events from servers in a cloud environment may be simpler than you think. Cloud servers are still servers, meaning that they produce logs and events as any in-house server. In this post we will be discussing few strategies and architectures to consider when planning a QRadar implementation with servers in the cloud.
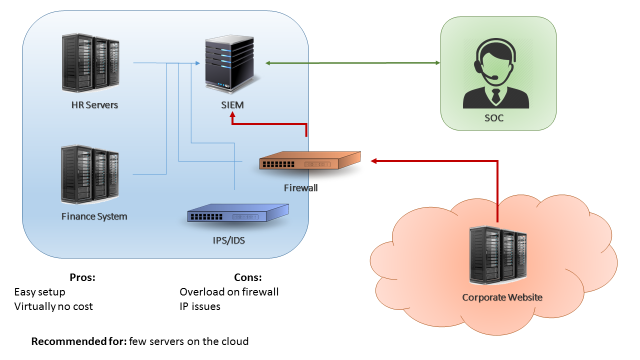
The first scenario is when you have just few servers in the cloud (less than 15% of your environment, or less than 500EPS coming from the cloud). A easy approach for this scenario can be simply configuring your cloud servers to send logs to your existing in-house QRadar collector (Figure 1). This can be accomplished by using a VPN between your cloud environment and your datacentre, or by configuring your firewalls to allow your cloud servers to send logs directly to your in-house collector. The benefits in this case are the fact that is a very easy setup and there’s virtually no costs. The downside on this design is that if your server generate a high number of events, your firewall/VPN could be overloaded.
The second scenario is when you have a substantial amount of servers in the cloud (between 30%-40% of your environment, or less than 5000 EPS). In this case, if you try to send all your events directly through a firewall or VPN you may overload the border network devices of your environment. The recommended approach in this case would be implementing a virtual collector/processor in your cloud environment (Figure 2). The cloud servers would send logs to your virtual collector/processor, which will parse the data locally and compress it before sending to the in-house SIEM collector. This architecture benefits from the fact that you will have an increased EPS capacity. Also, if your VPN dies or if the network is unstable you don’t lose events due to the fact the collector buffers the logs locally. In other hand, this architecture will have an extra cost (the additional collector) and, even with the traffic being compressed, it still may affect your firewall/VPN performance in case you’re monitoring a large quantity of servers.

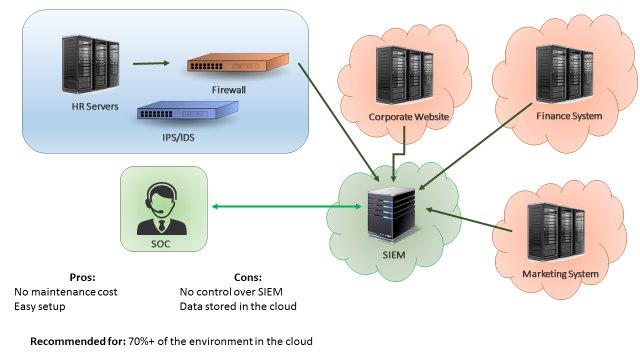
The third scenario is when most of your servers are in the cloud. In this case, a good approach would be having QRadar collectors (or even your whole QRadar infrastructure) deployed on the cloud, as seen on Figure 3. In this way, your border network devices will not be overloaded by logs sent from cloud servers to your internal SIEM. A similar approach would be having “QRadar as service”, which is a service from IBM where all the SIEM infrastructure is taken care by the IBM team. The advantages of having SIEM as a service is that you don’t need to worry about the SIEM maintenance and there’s little to none setup effort. The disadvantages is that your data will be stored in the IBM cloud environment, which for some companies may not be adequate.
Those are the three most common approaches when monitoring cloud servers with a SIEM solution. It is important to remember that each case is a case, meaning that each company should analyse their current and future environment before designing a SIEM implementation. You may find that a combination of the presented approaches may suit best your needs. The most important thing is remembering that monitoring servers in the cloud is as important as monitoring in-house servers.
Detecting ransomware with QRadar using behavioral analysis
Ransomware is one of the top trending concerns in any business; hundreds of business are seeing their data being encrypted even with the latest security solutions. As most of anti-virus solutions are signature based, they are not fully capable of detecting the latest ransomware strains. In this post we will be discussing how to configure QRadar to detect ransomware threats in real time by observing events’ behaviour.
Ransomware may seem a complex attack, but most of them are actually quite simple: The malware encrypts files and then shows a ransom message to the user. The objective of the attacker is to encrypt the files as fast as possible to maximize the impact (if the encryption is slow the user may notice and stop the attack before all the files gets encrypted), and that’s how we can detect the threat.
In a simple language, the encryption process consists in: open a file, read a file, write the encrypted file, close the file. If you are monitoring your servers with QRadar, every time a file is updated an event is generated. So if you detect a high volume of “file update” events in a short period of time, it may be a sign of a ransomware infection.
Based on that, to implement an effective ransomware monitoring capability on QRadar all you need to do is:
- Ensure file audit is enabled on your windows servers: You need to be able to see events such as “File open”, “File Update” and “File Delete”. Before creating any rule, search for those event names to make sure you are getting them. Please note that this can considerably increase your EPS rate, so if you have a large environment and you’re enabling file-access audit consider enabling it in stages and observing your EPS rate.
- Create an offense rule that detect multiple file updates: A good threshold is 500 file updates in a minute. If you see more than 500 file updates in less than a minute, that’s an indication that there is an automated process updating your files (which may be a sign of ransomware).
If you have any mitigation system (such as IBM BigFix or McAfee EPO), you can even trigger a mitigation action to stop the ransomware. For example with QRadar you can send a “process kill” request to IBM BigFix, which will quickly login into the machine and kill the ransomware process.
It is important to note that QRadar is detecting ransomware through system behaviour. This puts QRadar in advantage if compared to regular signature-based anti-virus solutions, since we will be capable of detecting “zero-day” ransomware, which anti-virus solutions may not have signature for it.
This post is based on a very interesting video series called “QRadar Stopping Ransomware” by Jose Bravo. If you want to see step-by-step of how to configure your SIEM to stop ransomware, you should check out his youtube channel.
Proactively identifying performance issues with the HCF plugin
In the last post, we talked about the Health Check Framework (HCF) and its benefits. Since I’ve been using the plugin for over a month I was able to collect useful performance information and identify some potential performance issues even before they occur. In this post, you will learn how to proactively monitor your system performance and prevent potential performance issues from happening.
First, you will need to install the Health Check Framework plugin. The installation process is quite straightforward: all you need is to go to your IBM app store on your QRadar environment, search for “Health Check Framework” and install it following the steps on the screen. With the plugin installed, you can start by browsing the plugin interface and extracting a report about your system performance. In this report, you will see a lot of details about your system, such as CPU Usage, Disk Usage, EPS, FPM, heavy reports, current users, etc.

In my case, we are planning to expand the scope of servers monitored by QRadar, so I wanted to understand if we would need any hardware upgrades. For testing purposes, I disabled the log collection of 30 Windows servers that were currently being monitored and I noticed that the RAM memory usage reduced by around 5% (see images below). Obviously, this number will vary according to the server usage, but this test gave me a rough estimation that for each 30 servers my RAM memory usage will increase around 5%. So with the help of the HCF plugin, I was able to identify hardware upgrades to accommodate the monitoring of new servers, avoiding system outages due to lack of resources during the scope expansion.


Even if you’re not planning to expand your scope, you can use historical performance data to proactively identify issues. For example, let’s say, your QRadar monitors a new e-commerce website. The number of logs you get depends on the traffic your website has. With the historical data, you will be able to identify a performance trend: as the e-commerce website becomes more popular, the EPS increases and the CPU/Memory usage also increases. With this data, you will be able to estimate at which point in time you will need a hardware upgrade, avoiding any unexpected system outages due to lack of resources.
Another very interesting data that I found in this report was the “Event Average Payload Size”, which as the name says, tells you the average size of logs received. This can be very useful to identify hard drive requirements when expanding your EPS.
Using the same plugin I was also able to identify heavy reports and rules that were severely impacting the performance of my QRadar environment. After reviewing and fixing the queries of the reports and rules, it was noticed a considerable reduction in the CPU usage.

Monitoring the performance of your system puts you in a proactive posture in relation to your environment. Being proactive means that you will not be firefighting issues as before, but instead, monitoring and planning upgrades ahead to avoid issues even before they happen.
QRadar Apps: Health Check Framework
One of the most interesting features introduced on QRadar 7.2.6 is the AppExchange, which allow you to install plugins (or also called, QRadar Apps) within just few clicks. Last week I came across a very interesting app called Health Check Framework (HCF) that allows you to perform health checks on your QRadar platform. What I found interesting is that the plugin brings you information that you would need to spend hours trying to find in the complicated QRadar log files or that you would need to be manually running scripts on the server. The plugin also creates for you real-time dashboards showing information around data compression, index file usage, EPS usage, and others.

The plugin, which can be easily installed through the IBM AppExchange, is developed by a company called Science Soft, you can check their app details in their website, but here’s the main features that caught my attention:
- HCF provides a 360-degree view of all essential characteristics of QRadar operation. It indicates deviations, which allows security officers to take urgent steps to fix them.
- QRadar health check can be both scheduled and started manually on demand, and its results are provided as a report.
- HCF assesses QRadar’s state with 60+ operational metrics that are configured into 25 health markers showing either ‘OK’ or ‘Failed’ and reported in an email to HCF subscribers.
- The reports describe how well the security system components are connected to QRadar and if there are security events that are not classified.
- Ability to create a system-health baseline using the called “health markers”, which are are like a snapshot of QRadar, allowing you to compare the health status over a period of time.
- ‘Failed’ markers are followed by recommendations on further actions.

The HCF app has been helping me to troubleshoot performance issues and helped me to proactively identify some issues (for example, that my server was using almost all of its RAM memory in a constant trend). The app also reduced the amount of time I spend analyzing the QRadar log files, so it may be useful for you to keep control of your SIEM environment and increase the ROI of your SIEM investment.
If you would like to know more about this plugin, check out the developer’s website or the IBM QRadar AppExchange! If you have used this app, tell us on the comments your experience!
- ← Previous
- 1
- 2
- 3
- …
- 7
- Next →